Business Outcomes Powered by IT
Fort Worth Outsourced IT Support & IT Services
Let our team at Inman Technologies provide you with the best IT support and solutions to increase your profitability and allow you to focus on growing your business.
Your Neighborhood IT Department
Why Choose Us
We Listen
We take a genuine approach to best understand your business by listening to your needs and simplifying the entire experience.
We Discover
We do a deeper dive into your current processes, network, and infrastructure to identify strengths, weaknesses, and overall IT needs.
We Recommend
We take our findings from the assessments and recommend an IT approach that will best support your business needs and goals.
We Improve
We keep your technology environment constantly improving as needed to help you maintain a competitive edge in your industry.
Client Success Stories

"I have had the good fortune to work with Inman Technologies for the past two years where they have managed and supported a full range of IT services from basic computer setup and software management to a complete overhaul or our servers and security protocols.
Above all, we have developed a relationship with Sean and his team due to their thoroughness and quick response to all our needs."
Bobby Snyder, President of Construction
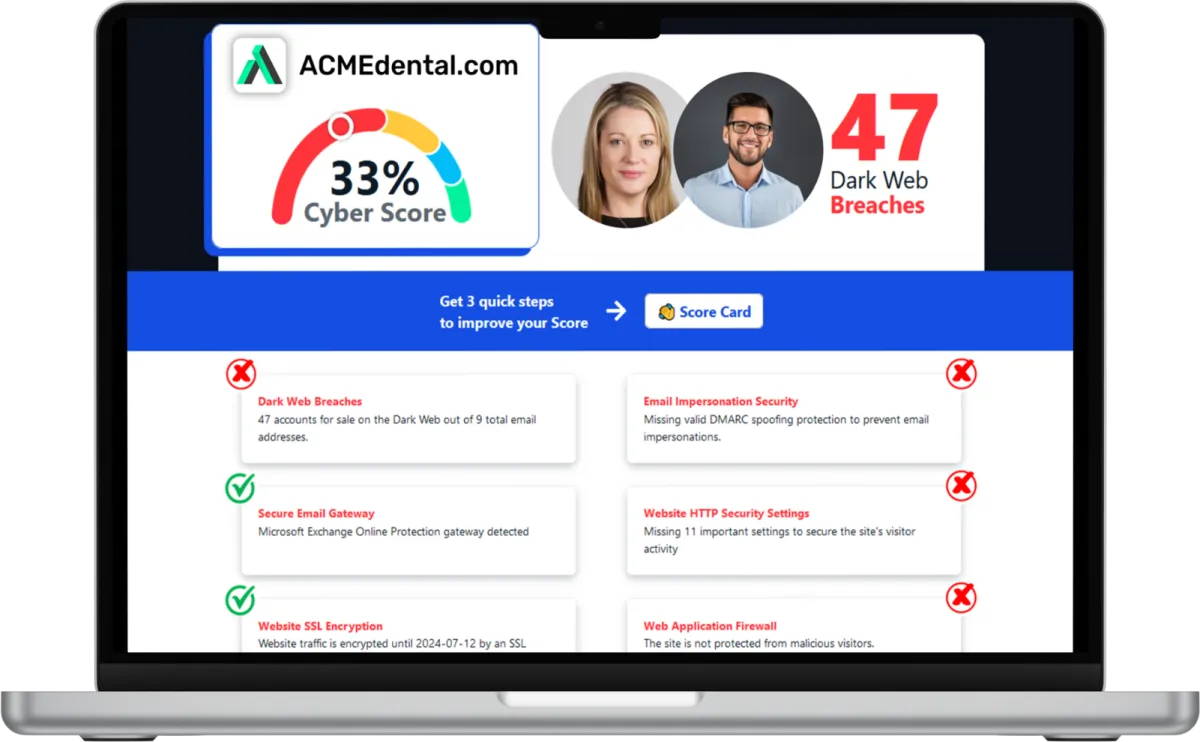
Want to see your Score? Get it in 30 seconds!
If You’ve Been Dealing with IT Challenges,
You’re Not Alone

Sean Inman
Founder & CEO
Inman Technologies is Here to Help.
Inman Technologies is a leading managed IT service provider in Fort Worth, TX, offering a comprehensive selection of outsourced IT support and IT services to businesses in Fort Worth, TX, and the surrounding areas, including Aledo, Willow Park, Hudson Oaks, and Weatherford, TX, and Oklahoma City and Edmond, OK. We specialize in providing IT support and Cybersecurity services to meet the unique needs of businesses.
Call 682-882-9344 today for comprehensive cybersecurity and managed IT services tailored to your needs.
Schedule an Appointment Today
Our Services
We monitor, maintain and manage your IT systems around-the-clock so you can focus on growing your business.
We provide robust protection against cyber threats, ensuring the confidentiality, integrity and availability of your data.
We offer assistance with any sort of IT project - ensuring it's completed on time and on budget.
Harness the Power of AI for Your Business
At Inman Technologies, we bring cutting-edge AI solutions to businesses of all sizes. Our AI as a Service offerings are designed to simplify your operations, enhance customer experiences, and drive measurable growth. From automating customer interactions to optimizing your marketing strategies, we deliver secure, tailored AI tools that make your business smarter and more efficient.
What Clients Say About Us
Partners and products we support to deliver unparalleled productivity:
Business Technology Insights
Explore expert insights, trends, and expert advice on the ever-evolving landscape of information technology. Dive in to discover how we leverage cutting-edge solutions to empower businesses and drive innovation.

9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks.

5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year.

Workspaces, a VPN & More – Learn the Newest Microsoft ...
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation.

The Hidden Cybersecurity Risk for Fort Worth Construction Companies: Your Vendors
Construction companies in Fort Worth, Arlington, Keller, and across North Texas rely heavily on vendors and subcontractors to complete projects.
Architects share their plans.
Engineers work together on documents.
Payroll providers handle payments.
Project management platforms keep important files.
Each partner introduces a potential digital vulnerability into your organization, underscoring the need for strategic oversight at the executive level.
If any vendor has weak cybersecurity, attackers can harm your company. This supply chain risk is a growing threat to Texas construction businesses, especially those managing multiple vendors and financial transactions.
Why Cybercriminals Target Construction Companies
Cybercriminals understand that construction companies handle large sums of money and depend on many subcontractors and vendors.
Rather than attacking a well-protected contractor directly, attackers often target smaller partners with weaker cybersecurity.
Once inside, they can access:
project documentation
financial workflows
vendor payment systems
shared cloud storage
email communications between partners
Major supply chain attacks, such as SolarWinds and MOVEit, demonstrate just how damaging these breaches can be.
Fort Worth area construction companies face these vulnerabilities daily.
How a Vendor Breach Can Impact Your Construction Business
If a vendor is compromised, your company can still suffer the consequences.
Financial Fraud
Construction companies are often targets of invoice fraud and wire transfer scams.
Attackers might impersonate vendors and redirect payments, sometimes stealing hundreds of thousands of dollars from a single project.
Project Delays
Cyber incidents can shut down important platforms like:
construction management software
blueprint storage systems
scheduling tools
document collaboration platforms
Even brief disruptions can delay schedules and raise project costs.
Loss of Client Trust
Developers and project owners expect contractors to keep sensitive information, including structural plans, safe.
financial details
contract documents
project timelines
A breach involving project data can harm relationships and future business opportunities.
Why Vendor Cybersecurity Risk Is High in Construction
Construction companies often work with many vendors at the same time, such as:
subcontractors
engineering firms
accounting providers
cloud software vendors
equipment suppliers
payroll companies
Unfortunately, many smaller vendors lack robust cybersecurity protections.
Common security weaknesses are:
Weak Password Practices
Using shared credentials and simple passwords is still common.
No Multi-Factor Authentication
Without multi-factor authentication, stolen passwords give attackers instant access.
Poor Access Control
Sometimes vendors keep system access long after a project is finished.
Unpatched Software
Outdated systems create easy targets for attackers.
Limited Security Training
Employees might accidentally click phishing emails that compromise accounts.
These weaknesses make vendors a major cybersecurity blind spot for construction companies.
How Fort Worth Construction Companies Can Assess Vendor Security
Cybersecurity should be a core criterion in vendor selection, on par with insurance and safety compliance.
Ask your vendors these important questions.
Do They Follow Security Standards?
Look for recognized frameworks such as:
SOC 2
ISO 27001
NIST cybersecurity controls
These show that they have organized security practices.
How Do They Protect Your Data?
Ask about things like:
encryption
secure cloud storage
backup and disaster recovery
How Do They Manage System Access:
multi-factor authentication
role-based permissions
monitoring of administrative accounts
What Happens If They Are Breached?
Your vendor should clearly explain:
breach notification timelines
incident response procedures
steps taken to protect your data
The best practice is to notify you within 24 to 72 hours.
5 Practical Ways Contractors Can Reduce Vendor Cybersecurity Risk
Construction companies can enhance security outcomes by implementing several key measures.
1. Build a Vendor Inventory
Make a list of every vendor who has access to:
financial systems
project management tools
internal documents
cloud storage platforms
Many companies find they have more digital access points than they thought they did.
2. Sort Vendors by Risk
Assign risk levels like:
Critical Risk
IT providers
project management platforms
accounting systems
payroll providers
Medium Risk
Subcontractors accessing shared files
engineering partners
document collaboration tools
Low Risk
marketing vendors
website providers
For high-risk vendors, conduct in-depth security reviews, ask for supporting documentation, and schedule regular assessments to ensure compliance with your cybersecurity requirements.
3. Add Cybersecurity Rules to Contracts
Vendor contracts should include rules like:
multi-factor authentication
secure data handling
breach notification obligations
cybersecurity insurance
These contractual protections align vendors with the executive team’s risk management objectives, helping safeguard organizational interests.
4. Limit Vendor Access
Follow the least privilege principle.
Vendors should have access only to the systems they need for their role and only while projects are active.
5. Keep an Eye on Vendors Regularly
Check vendor security on a regular basis.
Monitoring can detect:
vendor data breaches
compromised credentials
security rating changes
This helps spot risks before they affect your business.
Why Cybersecurity Matters More for Construction Bids
Developers, city officials, and major clients are increasingly reviewing cybersecurity practices before awarding projects.
Contractors with strong cybersecurity programs get benefits like:
eligibility for larger contracts
compliance with insurance requirements
stronger client confidence
reduced project risk
For construction leaders, cybersecurity is becoming a critical differentiator and a strategic lever for market advantage.
Local Cybersecurity Support for Fort Worth Construction Companies
Many construction businesses in Fort Worth, Arlington, Southlake, Keller, Burleson, and Weatherford don’t have their own cybersecurity teams.
A local managed IT partner can help by:
Assessing vendor cybersecurity risks
Securing project management platforms
Implementing access controls
Protecting financial transactions from fraud
Monitoring supply chain threats
Comprehensive vendor security oversight ensures your external ecosystem is protected, extending the executive mandate beyond internal controls.
Protect Your Construction Business from Vendor Cybersecurity Risk
Supply chain cybersecurity threats are growing fast, especially in industries like construction that depend on many vendors and subcontractors.
By actively managing vendor security, construction companies can protect:
project data
financial transactions
operational timelines
client trust
Robust executive-driven cybersecurity keeps projects on schedule and protects business interests.
Fort Worth Construction Companies: Strengthen Your Cybersecurity
Executives managing construction firms with vendor dependencies cannot overlook the strategic importance of vendor cybersecurity risk.
Inman Technologies helps construction companies in Fort Worth and North Texas secure their vendor networks and protect important project systems.
Our team specializes in helping contractors:
Identify vendor cybersecurity risks
Secure project management platforms
Prevent invoice fraud and payment scams
Implement cybersecurity best practices
Schedule a consultation today!
Click here ➡️ Free Construction Vendor Cybersecurity Checklist
Frequently Asked Questions
What are the benefits of cybersecurity services?
Cybersecurity services offer numerous advantages for businesses. They protect your sensitive data from unauthorized access, safeguard your systems from cyber threats, ensure compliance with industry regulations, and enhance the overall resilience of your IT infrastructure.
What are managed IT service providers?
Managed IT service providers handle your IT needs, allowing you to focus on your core business operations. They provide proactive IT support, network monitoring, data backup, cybersecurity, and other essential services to ensure the smooth functioning of your IT environment.
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What makes our IT Support different from other MSPs?
At Inman Technologies, we stand out as a premier outsourced IT support provider in Fort Worth through our unique approach to technology services. Unlike other providers, we don't believe in one-size-fits-all solutions or long-term contracts that lock you in. Instead, we offer:
✔️ Flexible Service Model
✔️ Comprehensive Support
✔️ Innovation Focus - AI-powered solutions
✔️ Local Expertise
Whether you're a small tax office or a growing enterprise, our outsourced IT support services provide the flexibility, expertise, and personal attention your business needs to thrive in today's digital landscape.
📅 Schedule an Appointment With Us to learn more about our unique approach to IT support.
Share Your IT Burdens With Us
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us on your side, develop customized security plans, stronger communication strategies, and a better plan for the future.
Click the button below to schedule your appointment. We’re ready to jumpstart your IT journey.