Business Outcomes Powered by IT
Fort Worth Outsourced IT Support & IT Services
Let our team at Inman Technologies provide you with the best IT support and solutions to increase your profitability and allow you to focus on growing your business.
Your Neighborhood IT Department
Why Choose Us
We Listen
We take a genuine approach to best understand your business by listening to your needs and simplifying the entire experience.
We Discover
We do a deeper dive into your current processes, network, and infrastructure to identify strengths, weaknesses, and overall IT needs.
We Recommend
We take our findings from the assessments and recommend an IT approach that will best support your business needs and goals.
We Improve
We keep your technology environment constantly improving as needed to help you maintain a competitive edge in your industry.
Client Success Stories

"I have had the good fortune to work with Inman Technologies for the past two years where they have managed and supported a full range of IT services from basic computer setup and software management to a complete overhaul or our servers and security protocols.
Above all, we have developed a relationship with Sean and his team due to their thoroughness and quick response to all our needs."
Bobby Snyder, President of Construction
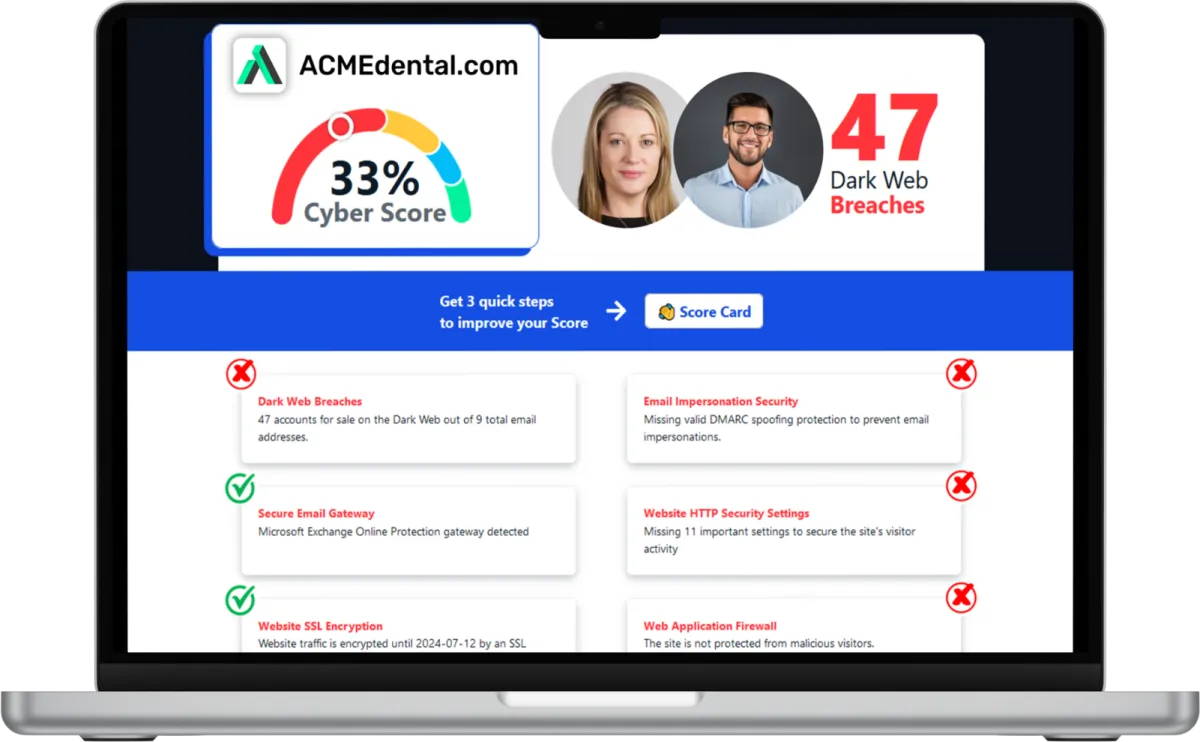
Want to see your Score? Get it in 30 seconds!
If You’ve Been Dealing with IT Challenges,
You’re Not Alone

Sean Inman
Founder & CEO
Inman Technologies is Here to Help.
Inman Technologies is a leading managed IT service provider in Fort Worth, TX, offering a comprehensive selection of outsourced IT support and IT services to businesses in Fort Worth, TX, and the surrounding areas, including Aledo, Willow Park, Hudson Oaks, and Weatherford, TX, and Oklahoma City and Edmond, OK. We specialize in providing IT support and Cybersecurity services to meet the unique needs of businesses.
Call 682-882-9344 today for comprehensive cybersecurity and managed IT services tailored to your needs.
Schedule an Appointment Today
Our Services
We monitor, maintain and manage your IT systems around-the-clock so you can focus on growing your business.
We provide robust protection against cyber threats, ensuring the confidentiality, integrity and availability of your data.
We offer assistance with any sort of IT project - ensuring it's completed on time and on budget.
Harness the Power of AI for Your Business
At Inman Technologies, we bring cutting-edge AI solutions to businesses of all sizes. Our AI as a Service offerings are designed to simplify your operations, enhance customer experiences, and drive measurable growth. From automating customer interactions to optimizing your marketing strategies, we deliver secure, tailored AI tools that make your business smarter and more efficient.
What Clients Say About Us
Partners and products we support to deliver unparalleled productivity:
Business Technology Insights
Explore expert insights, trends, and expert advice on the ever-evolving landscape of information technology. Dive in to discover how we leverage cutting-edge solutions to empower businesses and drive innovation.

9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks.

5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year.

Workspaces, a VPN & More – Learn the Newest Microsoft ...
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation.

The Third Place Work Policy Every Business Leader Will Need in 2026
How Coffee Shops and Coworking Spaces Can Create Cybersecurity Risks
Work now happens in many places, not just the office.
Employees today often work from coffee shops, coworking spaces, hotel lobbies, and job sites. These are often called “third places” meaning any work location that is not your office or your home.
These environments provide flexibility and convenience and can boost productivity.
However, they also introduce serious cybersecurity risks.
Without clear security standards for working outside the office, your business could unknowingly expose sensitive data, client information, and internal systems to cyberattacks.
This guide explains the policies and best practices business leaders need to protect their company while supporting a modern hybrid workforce.
The Hidden Risks of Third-Place Work
Public Wi-Fi Is a Major Vulnerability
Most public Wi-Fi networks are not built with business security in mind.
Public Wi-Fi includes any free or shared network outside of your company’s secured office environment, such as:
Coffee shops (Starbucks, local cafés, etc.)
Coworking spaces (WeWork, shared offices, hot desks)
Hotels and conference centers
Airports and airline lounges
Restaurants and fast-food chains
Libraries and community centers
Job sites using temporary or shared internet connections
Client guest Wi-Fi networks
Even though these networks are convenient, they are often unsecured or shared with dozens (or hundreds) of strangers at the same time.
Attackers can exploit these environments to:
Intercept login credentials
Monitor company email traffic
Steal confidential project data
Launch ransomware attacks through compromised devices
Even when Wi-Fi requires a password, that password is often posted publicly or shared with everyone in the building.
For businesses, just one insecure connection can quickly lead to a costly data breach.
Core Elements of a Third Place Security Policy
A good third place work policy should be simple, easy to enforce, and based on proven security controls.
1. Mandatory Secure Remote Access
Every employee working outside the office should use secure access tools.
Key requirements include:
VPN (Virtual Private Network)
Encrypts all traffic so attackers cannot intercept sensitive information.Zero Trust Network Access (ZTNA)
A modern alternative to VPN that limits access based on identity, device health, and location.
Best practice is to have VPN or secure access turn on automatically when connecting to any untrusted network.
2. Device Security and Endpoint Protection
Working in third places is only safe if the device is protected.
Your policy should require:
Company-managed laptops and phones (not personal devices)
Full disk encryption enabled
Automatic patching and updates
Advanced endpoint protection (EDR)
Standardized device management makes sure every employee starts with the same level of security.
3. Physical and Visual Security
Cybersecurity is not only about digital threats.
Public places also bring physical security risks.
Employees should follow practices like:
Using privacy screens to prevent shoulder surfing
Locking devices when stepping away
Never leaving laptops unattended
Using cable locks in coworking spaces
If a laptop is stolen, it can give someone direct access to your systems.
Behavior Controls That Reduce Risk
Technology is not enough on its own. Good security depends on daily habits.
Communication Discipline in Public
Employees should not discuss sensitive business topics in public, especially during phone calls.
Encourage:
Using headphones
Taking private calls away from crowds
Not having open conversations about clients, finances, or internal projects
Limit High-Risk Actions on Public Networks
Even with security measures, public Wi-Fi should always be considered high risk.
Employees should avoid accessing:
Payroll systems
Banking portals
Admin dashboards
Sensitive client documentation
If employees must access these systems, they should use strong authentication.
Executive-Level Policy Components You Need
A third place security policy should make expectations clear.
Every business policy should include:
What qualifies as a third place workspace
Approved tools (VPN, MFA, endpoint protection)
Employee responsibilities
Incident reporting procedures
Compliance requirements
Annual review and updates
A policy is only effective if it is simple to follow and enforce.
Strengthening Control With Authentication and Monitoring
Multi-Factor Authentication (MFA)
MFA is one of the best ways to protect against stolen passwords.
Even if someone’s credentials are stolen, MFA can prevent attackers from gaining access.
Best practices include:
Require MFA for all cloud apps, email, and remote access
Use app-based authentication or hardware keys
Try not to use SMS-only MFA if you can avoid it
Monitoring and Detection
Businesses should deploy systems that can detect:
Unusual remote login behavior
Devices connecting from risky locations
Suspicious access attempts
Modern cybersecurity focuses on preventing problems before they happen.
Training: The Human Firewall
Policies do not work without proper training.
Employees need real-world awareness of:
Phishing attacks
Fake Wi-Fi networks
Social engineering tactics
Secure habits while traveling or working remotely
With regular training, your employees become a security strength instead of a weakness.
Construction and Field Team Considerations
For industries like construction, employees often work from:
Job trailers
Temporary networks
Client offices
Field locations with limited infrastructure
Recommended best practices include:
Using secure mobile hotspots instead of open Wi-Fi
Standardizing device onboarding for job site teams
Ensuring cloud platforms have strong access controls and logging
Field teams need just as much protection as office staff.
Third Place Security Checklist
Use this quick checklist to see if you are ready:
VPN is mandatory on public networks
MFA is enforced across all critical systems
Devices are encrypted and centrally managed
Endpoint security is active on all laptops
Employees have completed security training
Incident reporting procedures are documented
Policy is reviewed at least annually
Conclusion: Flexibility Without Added Risk
Hybrid work is here to stay.
However, flexibility should not come at the expense of security.
By setting a clear third place work policy, using secure access controls, and training employees well, your business can support modern work without increasing cyber risks.
Secure Your Remote Workforce With Inman Technologies
At Inman Technologies, we help business leaders protect their teams, devices, and data, whether employees work in the office, at home, or from a coffee shop.
Schedule a consultation with our cybersecurity experts to:
Build or audit your third place security policy
Deploy secure remote access tools
Protect field teams
Train employees against real-world threats
Or download our Remote Work Security Policy for business owners.
Contact Inman Technologies today to secure your workforce, no matter where work takes place.
Frequently Asked Questions
What are the benefits of cybersecurity services?
Cybersecurity services offer numerous advantages for businesses. They protect your sensitive data from unauthorized access, safeguard your systems from cyber threats, ensure compliance with industry regulations, and enhance the overall resilience of your IT infrastructure.
What are managed IT service providers?
Managed IT service providers handle your IT needs, allowing you to focus on your core business operations. They provide proactive IT support, network monitoring, data backup, cybersecurity, and other essential services to ensure the smooth functioning of your IT environment.
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What makes our IT Support different from other MSPs?
At Inman Technologies, we stand out as a premier outsourced IT support provider in Fort Worth through our unique approach to technology services. Unlike other providers, we don't believe in one-size-fits-all solutions or long-term contracts that lock you in. Instead, we offer:
✔️ Flexible Service Model
✔️ Comprehensive Support
✔️ Innovation Focus - AI-powered solutions
✔️ Local Expertise
Whether you're a small tax office or a growing enterprise, our outsourced IT support services provide the flexibility, expertise, and personal attention your business needs to thrive in today's digital landscape.
📅 Schedule an Appointment With Us to learn more about our unique approach to IT support.
Share Your IT Burdens With Us
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us on your side, develop customized security plans, stronger communication strategies, and a better plan for the future.
Click the button below to schedule your appointment. We’re ready to jumpstart your IT journey.