Business Outcomes Powered by IT
Fort Worth Outsourced IT Support & IT Services
Let our team at Inman Technologies provide you with the best IT support and solutions to increase your profitability and allow you to focus on growing your business.
Your Neighborhood IT Department
Why Choose Us
We Listen
We take a genuine approach to best understand your business by listening to your needs and simplifying the entire experience.
We Discover
We do a deeper dive into your current processes, network, and infrastructure to identify strengths, weaknesses, and overall IT needs.
We Recommend
We take our findings from the assessments and recommend an IT approach that will best support your business needs and goals.
We Improve
We keep your technology environment constantly improving as needed to help you maintain a competitive edge in your industry.
Client Success Stories

"I have had the good fortune to work with Inman Technologies for the past two years where they have managed and supported a full range of IT services from basic computer setup and software management to a complete overhaul or our servers and security protocols.
Above all, we have developed a relationship with Sean and his team due to their thoroughness and quick response to all our needs."
Bobby Snyder, President of Construction
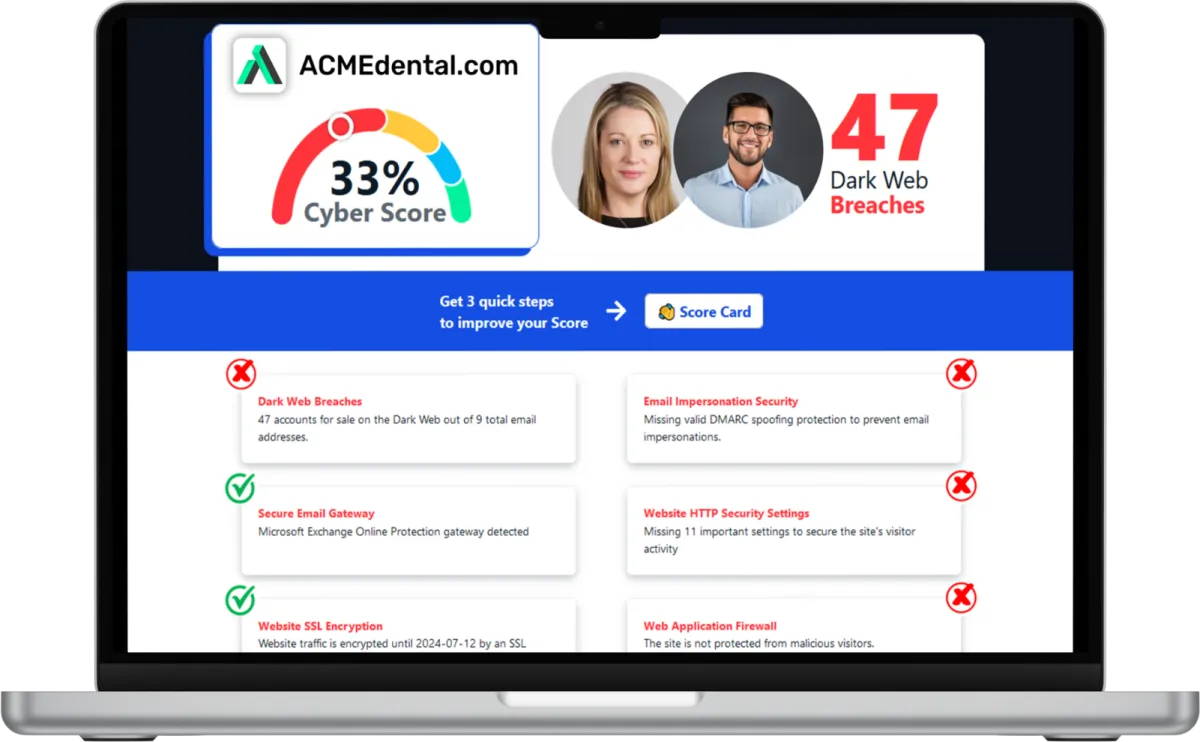
Want to see your Score? Get it in 30 seconds!
If You’ve Been Dealing with IT Challenges,
You’re Not Alone

Sean Inman
Founder & CEO
Inman Technologies is Here to Help.
Inman Technologies is a leading managed IT service provider in Fort Worth, TX, offering a comprehensive selection of outsourced IT support and IT services to businesses in Fort Worth, TX, and the surrounding areas, including Aledo, Willow Park, Hudson Oaks, and Weatherford, TX, and Oklahoma City and Edmond, OK. We specialize in providing IT support and Cybersecurity services to meet the unique needs of businesses.
Call 682-882-9344 today for comprehensive cybersecurity and managed IT services tailored to your needs.
Schedule an Appointment Today
Our Services
We monitor, maintain and manage your IT systems around-the-clock so you can focus on growing your business.
We provide robust protection against cyber threats, ensuring the confidentiality, integrity and availability of your data.
We offer assistance with any sort of IT project - ensuring it's completed on time and on budget.
Harness the Power of AI for Your Business
At Inman Technologies, we bring cutting-edge AI solutions to businesses of all sizes. Our AI as a Service offerings are designed to simplify your operations, enhance customer experiences, and drive measurable growth. From automating customer interactions to optimizing your marketing strategies, we deliver secure, tailored AI tools that make your business smarter and more efficient.
What Clients Say About Us
Partners and products we support to deliver unparalleled productivity:
Business Technology Insights
Explore expert insights, trends, and expert advice on the ever-evolving landscape of information technology. Dive in to discover how we leverage cutting-edge solutions to empower businesses and drive innovation.

9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks.

5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year.

Workspaces, a VPN & More – Learn the Newest Microsoft ...
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation.

The Deepfake CEO Scam: When Voice Cloning Becomes the New BEC Playbook
How the small & medium sized businesses can mitigate risk through verification processes, proactive IT measures, and updated security training.
Imagine you get a call from your “CEO.”
The voice is accurate, the cadence familiar, and the request urgent: approve a wire, purchase gift cards, share payroll data, or send a client file “before the deadline hits.”
Everything appears normal until you discover the caller was not your executive.
AI-driven voice cloning has made executive impersonation faster, less expensive, and more convincing than traditional fraud attempts. For many organizations, it represents the next evolution of Business Email Compromise (BEC), now occurring by phone rather than email.
At Inman Technologies, we observe a clear trend: attackers are moving from targeting systems to pressuring individuals. The most effective defense is not intuition, but a robust process.
What is a “Deepfake CEO” voice scam?
A “Deepfake CEO” scam is a type of voice phishing (vishing) in which criminals use AI to imitate a leader’s voice and manipulate employees into taking high-risk actions, typically involving money, sensitive data, or account access.
This approach achieves the same goals as traditional BEC attacks, but uses a more persuasive delivery method. (Grobman, 2023)
Common targets include:
Accounting and finance teams (wires, ACH changes, invoice approvals)
HR (W-2s, payroll updates, direct deposit changes)
IT or operations (password resets, MFA changes, vendor access)
Executive assistants and office managers (gift cards, urgent purchases)
Why voice cloning works when email scams fail
Most organizations have invested in email filtering, domain protections, and spam controls. These measures are effective, particularly against older BEC techniques such as spoofing and phishing links.
Voice scams bypass many of these protections because:
Caller ID can be spoofed.
A phone call creates real-time pressure.
Employees are conditioned to respond quickly to leadership.
The attack exploits authority and urgency, not technical weakness.
Employees can scrutinize emails, but when a familiar voice demands immediate action, individuals often comply first and verify later.
This is the vulnerability.
How attackers get the voice
A private recording studio is not required to be at risk.
Attackers can capture voice samples from:
Company videos and webinars
Podcasts and interviews
Sales presentations posted online
Social media clips and stories
Voicemail greetings
With sufficient audio samples, widely available tools can generate a convincing imitation capable of delivering a scripted request.
Why “just listen carefully” is not a strategy
Some deepfake audio contains obvious flaws, but many do not.
Even when a fake voice sounds slightly unnatural, individuals often overlook discrepancies, especially under stress. Expecting someone to detect a deepfake in real time is comparable to asking them to identify a forged signature while a “CEO” is speaking urgently on the phone.
This is why the most effective mitigation is procedural:
If a request involves money, credentials, or sensitive data, verification needs to be mandatory.
The controls that actually stop voice-clone fraud
To reduce risk without hindering business operations, focus on controls that are simple, repeatable, and enforceable.
1) Build a “two-channel” rule for sensitive requests
If a request is received through one channel, such as a phone call, confirm it through another channel, such as Teams, a known email thread, internal ticketing, or a verified call-back number.
Examples:
Wire transfer request by phone → confirm in Teams with the executive’s verified account
Vendor banking change → confirm via a known contact method + documented approval workflow
Sensitive data request → require a written request through an approved system
2) Use call-back verification—every time
Do not continue the call.
Hang up and call back using:
a number in your directory, or
a previously verified number, not a number provided during the call
This single practice can prevent many real-world impersonation attempts.
3) Tighten payment and change-control processes
Voice scams often succeed because exceptions to established procedures are easily made.
Establish rules such as:
No payment changes without two approvals
No new vendor setup without verification + documentation
No banking changes without out-of-band confirmation
No urgent exceptions without written justification and a second approver
4) Train for modern social engineering, not last decade’s phishing
Security awareness training should include vishing simulations and realistic scenarios for:
finance approvals
HR record requests
password/MFA reset attempts
“executive emergency” pressure tactics
Training is most effective when it is role-based and aligned with actual workflows, rather than relying on generic videos that are easily forgotten. (Jacobs et al., n.d.)
5) Treat identity as a security control (not an assumption)
Many organizations still trust identity signals that are easy to fake:
caller ID
familiar voice
email display name
“sent from iPhone” style cues
A modern approach assumes identity can be spoofed and requires verification for all high-risk actions.
Business impact: it’s not just money
Voice cloning and deepfake content can cause issues that extend well beyond fraudulent transfers:Data exposure and compliance issues
Reputational damage if fake recordings circulate
Legal liability tied to mishandled information
Operational disruption while you investigate and recover
For business owners, this is fundamentally a business continuity issue. A single rushed decision can result in days or weeks of disruption and remediation.
A practical starting point for Texas businesses
To implement a straightforward plan quickly, begin with the following steps:
Define what counts as a high-risk request (money, credentials, sensitive data)
Require two-channel verification for those requests
Document the workflow and ensure it is mandatory
Conduct brief, realistic training sessions for the teams most at risk
Review incident response and communication procedures for deepfake scenarios
Next step (low effort, high value)
If you’d like a clearer picture of where your organization may be exposed to Business Email Compromise (BEC), vishing, or executive impersonation, Inman Technologies can help.
We work with Texas businesses to identify real-world risk points and implement practical verification workflows that align with how your team already operates—without adding unnecessary friction or slowing down the business.
In many cases, a short, focused assessment is enough to uncover the gaps attackers target first.
Schedule time with our team to review your current processes and strengthen your defenses before an incident forces the issue.
Frequently Asked Questions
What are the benefits of cybersecurity services?
Cybersecurity services offer numerous advantages for businesses. They protect your sensitive data from unauthorized access, safeguard your systems from cyber threats, ensure compliance with industry regulations, and enhance the overall resilience of your IT infrastructure.
What are managed IT service providers?
Managed IT service providers handle your IT needs, allowing you to focus on your core business operations. They provide proactive IT support, network monitoring, data backup, cybersecurity, and other essential services to ensure the smooth functioning of your IT environment.
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What makes our IT Support different from other MSPs?
At Inman Technologies, we stand out as a premier outsourced IT support provider in Fort Worth through our unique approach to technology services. Unlike other providers, we don't believe in one-size-fits-all solutions or long-term contracts that lock you in. Instead, we offer:
✔️ Flexible Service Model
✔️ Comprehensive Support
✔️ Innovation Focus - AI-powered solutions
✔️ Local Expertise
Whether you're a small tax office or a growing enterprise, our outsourced IT support services provide the flexibility, expertise, and personal attention your business needs to thrive in today's digital landscape.
📅 Schedule an Appointment With Us to learn more about our unique approach to IT support.
Share Your IT Burdens With Us
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us on your side, develop customized security plans, stronger communication strategies, and a better plan for the future.
Click the button below to schedule your appointment. We’re ready to jumpstart your IT journey.