Business Outcomes Powered by IT
Fort Worth Outsourced IT Support & IT Services
Let our team at Inman Technologies provide you with the best IT support and solutions to increase your profitability and allow you to focus on growing your business.
Your Neighborhood IT Department
Why Choose Us
We Listen
We take a genuine approach to best understand your business by listening to your needs and simplifying the entire experience.
We Discover
We do a deeper dive into your current processes, network, and infrastructure to identify strengths, weaknesses, and overall IT needs.
We Recommend
We take our findings from the assessments and recommend an IT approach that will best support your business needs and goals.
We Improve
We keep your technology environment constantly improving as needed to help you maintain a competitive edge in your industry.
Client Success Stories

"I have had the good fortune to work with Inman Technologies for the past two years where they have managed and supported a full range of IT services from basic computer setup and software management to a complete overhaul or our servers and security protocols.
Above all, we have developed a relationship with Sean and his team due to their thoroughness and quick response to all our needs."
Bobby Snyder, President of Construction
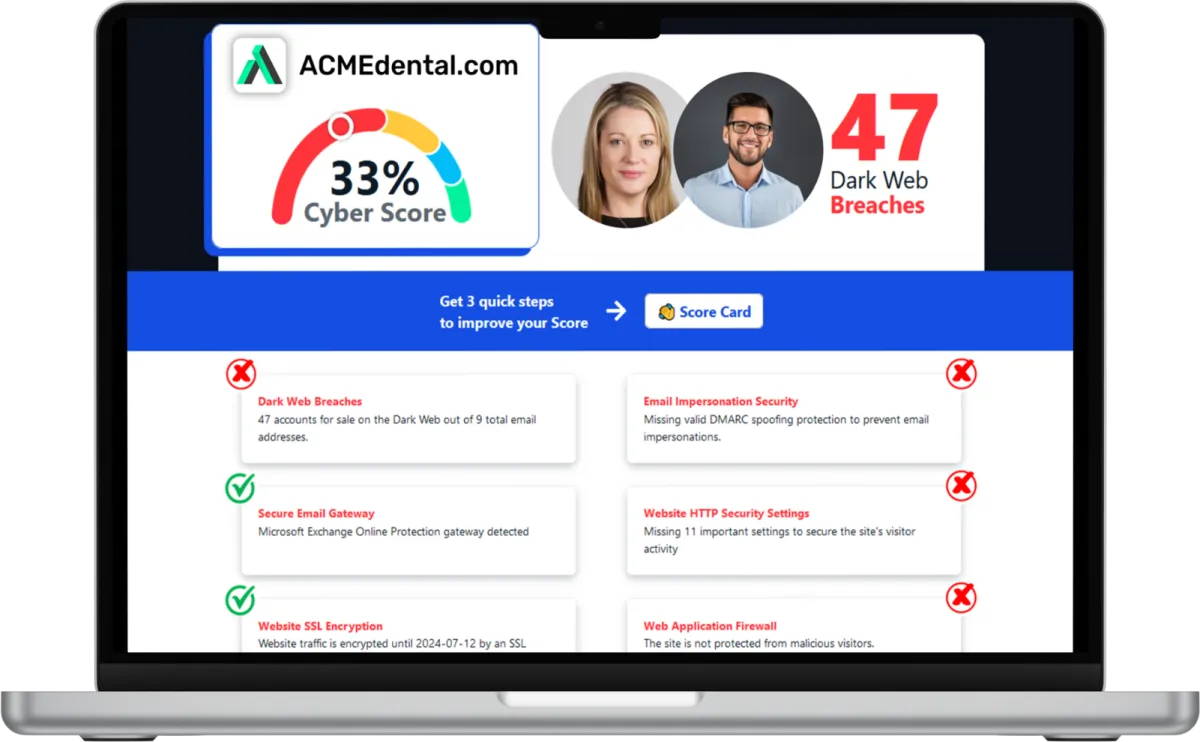
Want to see your Score? Get it in 30 seconds!
If You’ve Been Dealing with IT Challenges,
You’re Not Alone

Sean Inman
Founder & CEO
Inman Technologies is Here to Help.
Inman Technologies is a leading managed IT service provider in Fort Worth, TX, offering a comprehensive selection of outsourced IT support to businesses in Fort Worth, TX, and the surrounding areas, including Aledo, Willow Park, Hudson Oaks, Weatherford, TX, and Oklahoma City and Edmond, OK. We specialize in providing IT support and Cybersecurity services to meet the unique needs of businesses.
Call 682-882-9344 today for IT support tailored to your needs.
Schedule an Appointment Today
Our Services
We monitor, maintain and manage your IT systems around-the-clock so you can focus on growing your business.
We provide robust protection against cyber threats, ensuring the confidentiality, integrity and availability of your data.
We offer assistance with any sort of IT project - ensuring it's completed on time and on budget.
Harness the Power of AI for Your Business
At Inman Technologies, we bring cutting-edge AI solutions to businesses of all sizes. Our AI as a Service offerings are designed to simplify your operations, enhance customer experiences, and drive measurable growth. From automating customer interactions to optimizing your marketing strategies, we deliver secure, tailored AI tools that make your business smarter and more efficient.
What Clients Say About Us
Partners and products we support to deliver unparalleled productivity:
Business Technology Insights
Explore expert insights, trends, and expert advice on the ever-evolving landscape of information technology. Dive in to discover how we leverage cutting-edge solutions to empower businesses and drive innovation.

9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks.

5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year.

Workspaces, a VPN & More – Learn the Newest Microsoft ...
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation.

Why SMS MFA Is No Longer Secure for Your Business (And What to Use Instead)
For years, business owners were advised:
“Turn on MFA, and you’ll be protected.”
That advice was appropriate then.
However, the threat landscape has evolved. If your company still relies on SMS codes for multi-factor authentication (MFA), you may have a false sense of security.
For construction firms, professional services, and growing businesses in Fort Worth, identity attacks are the top entry point for cybercriminals. SMS-based MFA remains a weak link.
Here’s why and what modern businesses should use instead.
The Problem: SMS MFA Was Never Designed for Security
SMS-based MFA (the 6-digit codes sent to your phone) was designed for convenience, not security.
Although better than passwords alone, SMS MFA has critical weaknesses:
It relies on outdated telecom infrastructure (SS7)
Text messages can be intercepted or redirected
It’s vulnerable to phishing in real time
It can be defeated through SIM swapping attacks
Attackers are aware of these vulnerabilities.
Real-World Example
A construction firm CFO receives a fake Microsoft 365 login page. They enter:
Email
Password
SMS code
Within seconds, the attacker logs in, having captured all credentials in real time.
This leads to:
Wire fraud
Vendor impersonation
Payroll redirection
Ransomware
We hear of incidents occurring daily across Texas.
SIM Swapping: A Silent Business Threat
One of the most dangerous threats to SMS MFA is SIM swapping.
Here’s how it works:
An attacker gathers publicly available information about you.
They call your mobile carrier pretending to be you.
They claim they lost their phone and request that your number be transferred.
Your phone goes offline.
The attacker now receives your calls and SMS MFA codes.
No malware is required.
No sophisticated hacking tools are needed.
Only social engineering tactics are used.
This poses a significant risk to executives, accounting teams, and project managers with access to financial systems.
The Shift: Phishing-Resistant MFA as the New Standard
For effective protection today, phishing-resistant MFA is essential.
These methods:
Cannot be replayed by attackers
Are tied to a specific website domain
Do not rely on SMS
Cannot be approved accidentally
The gold standard relies on FIDO2 and passkey authentication.
Here are your options.
Modern MFA Options Every Business Should Consider
1. Hardware Security Keys (Highest Security Level)
Physical devices such as YubiKeys that:
Plug into a USB port or tap via NFC
Perform a cryptographic handshake with the login service
Cannot be intercepted over the internet
Benefits:
Immune to phishing
Immune to SIM swapping
No codes to type
Ideal for executives and administrators.
This should be mandatory for privileged accounts such as owners, controllers, and IT administrators.
2. Authenticator Apps with Number Matching Feature
Examples include:
Microsoft Authenticator
Google Authenticator
Generate codes locally on the device, not over SMS.
Modern versions include number matching, which prevents “MFA fatigue” attacks where users are spammed with push notifications until they approve.
This significantly reduces risk compared to SMS-based MFA.
3. Passkeys (The Future of Business Authentication)
Passkeys eliminate the need for passwords entirely.
They utilize:
Device-based cryptographic keys
Biometrics (Face ID, fingerprint)
Secure cloud synchronization
Why this matters for businesses:
No password resets
No phishing risk
Reduced IT support tickets
Provides a seamless user experience
Microsoft 365, Google Workspace, and many enterprise platforms now support passkeys.
Why This Matters
Most firms are prime targets due to:
Large wire transfers are common
Vendor changes happen frequently
Field teams access cloud systems remotely
Email compromise leads to payment fraud
SMS MFA is insufficient to protect:
Microsoft 365
Accounting systems
Project management software
Banking portals
If your authentication is vulnerable to social engineering, your financial controls are at risk.
A Practical Roadmap to Upgrading Your MFA
We recommend Fort Worth businesses approach this as follows:
Step 1: Identify High-Risk Accounts
Owners
Executives
Accounting
IT admins
Anyone with wire transfer access
Step 2: Eliminate SMS MFA for Privileged Users
Replace SMS authentication immediately with:
Hardware keys, or
Authenticator apps with number matching
Step 3: Enable Phishing-Resistant Policies in Microsoft 365
Disable legacy authentication
Require compliant devices
Enforce conditional access policies
Step 4: Train Your Team Effectively
Explain:
What SIM swapping is
How phishing works
Why approvals should never be rushed
Security is effective only when users understand the reasons behind changes.
The Cost of Doing Nothing
Many companies retain SMS MFA because:
“It’s already enabled.”
“It checks the compliance box.”
“We’ve never had a breach.”
However, the reality is:
The average business email compromise (BEC) attack costs six figures.
The cost of upgrading authentication is minimal compared to the expense of a single fraudulent wire transfer.
Upgrading identity security offers one of the highest returns on investment in cybersecurity.
FAQ
Is SMS MFA better than no MFA?
Yes, but it is no longer sufficient to protect financial or administrative accounts.
What is phishing-resistant MFA?
Authentication that cannot be intercepted, replayed, or accidentally approved, typically using hardware keys or passkeys.
Are passkeys secure for businesses?
Yes. They rely on public-key cryptography and are currently among the strongest authentication methods available.
Inman Technologies Call to Action
Ready to Remove SMS MFA from Your Business?
If you still use text-message codes to protect Microsoft 365, banking, or project management systems, now is the time to upgrade.
At Inman Technologies, we help Fort Worth construction companies and growing businesses implement:
Phishing-resistant MFA
Secure Microsoft 365 configurations
Conditional access policies
Executive-level identity protection
Ongoing cybersecurity monitoring
Do not wait until a SIM swap or phishing attack compromises your financial systems.
Schedule a Security Consultation Today
Your authentication system is your front door. Let’s make sure it’s locked properly.
Frequently Asked Questions
What are the benefits of cybersecurity services?
Cybersecurity services offer numerous advantages for businesses. They protect your sensitive data from unauthorized access, safeguard your systems from cyber threats, ensure compliance with industry regulations, and enhance the overall resilience of your IT infrastructure.
What are managed IT service providers?
Managed IT service providers handle your IT needs, allowing you to focus on your core business operations. They provide proactive IT support, network monitoring, data backup, cybersecurity, and other essential services to ensure the smooth functioning of your IT environment.
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What makes our IT Support different from other MSPs?
At Inman Technologies, we stand out as a premier outsourced IT support provider in Fort Worth through our unique approach to technology services. Unlike other providers, we don't believe in one-size-fits-all solutions or long-term contracts that lock you in. Instead, we offer:
✔️ Flexible Service Model
✔️ Comprehensive Support
✔️ Innovation Focus - AI-powered solutions
✔️ Local Expertise
Whether you're a small tax office or a growing enterprise, our outsourced IT support services provide the flexibility, expertise, and personal attention your business needs to thrive in today's digital landscape.
📅 Schedule an Appointment With Us to learn more about our unique approach to IT support.
Share Your IT Burdens With Us
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us on your side, develop customized security plans, stronger communication strategies, and a better plan for the future.
Click the button below to schedule your appointment. We’re ready to jumpstart your IT journey.